https://vlang.io/
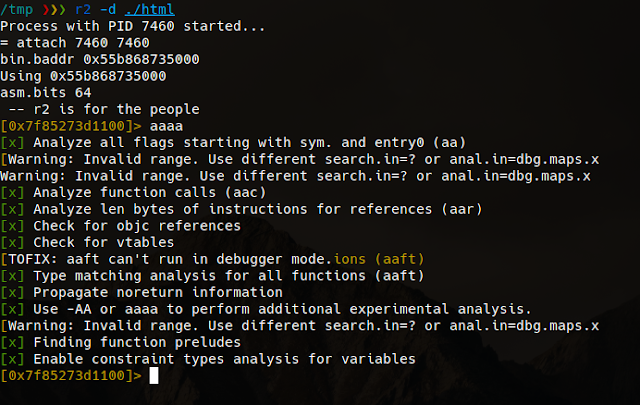
After open the binary with radare in debug mode "-d" we proceed to do the binary recursive analysis with "aaaa" the more a's the more deep analys.
The function names are modified when the binary is crafted, if we have a function named hello in a module named main we will have the symbol main__hello, but we can locate them quicly thanks to radare's grep done with "~" token in this case applied to the "afl" command which lists all the symbols.
Being in debug mode we can use "d*" commands, for example "db" for breakpointing the function and then "dc" to start or continue execution.
Let's dissasemble the function with "pD" command, it also displays the function variables and arguments as well, note also the xref "call xref from main"
Let's take a look to the function arguments, radare detect's this three 64bits registers used on the function.
Actually the function parameter is rsi that contains a testing html to test the href extraction algorithm.
The string structure is quite simple and it's plenty of implemented methods.
With F8 we can step over the code as we were in ollydbg on linux.
Note the rip marker sliding into the code.
We can recognize the aray creations, and the s.index_after() function used to find substrings since a specific position.
If we take a look de dissasembly we sill see quite a few calls to tos3() functions.
Those functions are involved in string initialization, and implements safety checks.
- tos(string, len)
- tos2(byteptr)
- tos3(charptr)
In this case I have a crash in my V code and I want to know what is crashing, just continue the execution with "dc" and see what poits the rip register.
In visual mode "V" we can see previous instructions to figure out the arguments and state.
We've located the crash on the substring operation which is something like "s2 := s1[a..b]" probably one of the arguments of the substring is out of bounds but luckily the V language has safety checks and is a controlled termination:
Switching the basic block view "space" we can see the execution flow, in this case we know the loops and branches because we have the code but this view also we can see the tos3 parameter "href=" which is useful to locate the position on the code.
When it reach the substr, we can see the parameters with "tab" command.
Looking the implementation the radare parameter calculation is quite exact.
Let's check the param values:
so the indexes are from 0x0e to 0x24 which are inside the buffer, lets continue to next iteration,
if we set a breakpoint and check every iteration, on latest iteration before the crash we have the values 0x2c to 0x70 with overflows the buffer and produces a controlled termination of the v compiled process.
More articles
- Computer Hacker
- Hack Tool Apk
- Hacker Tools For Windows
- Hack Tools Mac
- Nsa Hack Tools
- Tools Used For Hacking
- Hacker Tools 2020
- Hacker Security Tools
- Hacker Tools For Windows
- Hacker Tools List
- Pentest Tools For Windows
- Hack Tools Github
- Hacking Tools For Windows
- Hacker Tools Free
- Hacking Tools For Pc
- Hacker Tools 2020
- Pentest Tools Open Source
- Tools For Hacker
- Top Pentest Tools
- Pentest Tools Nmap
- Hacking Tools For Mac
- Hack Tools Github
- Hackrf Tools
- Hacker Tools For Mac
- Hacker Tools Free Download
- Pentest Tools Find Subdomains
- Hack And Tools
- Hacker Tools 2020
- Hacker Tools Mac
- Easy Hack Tools
- Hack App
- Hackrf Tools
- New Hack Tools
- Pentest Tools For Ubuntu
- Hacker Tools Github
- Pentest Tools For Windows
- Hacking Tools Free Download
- Android Hack Tools Github
- Game Hacking
- Hack Tools For Windows
- Pentest Tools Github
- Hacking Tools Online
- Free Pentest Tools For Windows
- Hacker Tools Github
- Hacker Tools For Pc
- Pentest Tools Open Source
- Hacker Search Tools
- Pentest Tools
- Pentest Tools Apk
- Hack Tools For Mac
- Pentest Tools Online
- Hacker Tools Free Download
- Hack Tools Mac
- Hacking Tools Windows
- Pentest Automation Tools
- New Hack Tools
- Hacker Tools Github
- How To Install Pentest Tools In Ubuntu
- Hacker Tools Linux
- Hacking Tools 2019
- Physical Pentest Tools
- Hacking Tools Windows 10
- Hack Tools Online
- Hacker Tools
- Hacking Tools For Pc
- Hack Website Online Tool
- Pentest Tools
- Underground Hacker Sites
- Hack App
- Hacker Tools Online
- Pentest Tools For Mac
- Hacking Tools Pc
- Hacker Tools For Mac
- Hacker Tools Github
- Hacking Tools Free Download
- Black Hat Hacker Tools
- Hacking Tools And Software
- Hacker Tools 2019
- Pentest Tools For Android
- Hacker Tools Online
- Top Pentest Tools
- Physical Pentest Tools
- Hacking Tools Kit
- Hack Tool Apk
- Hacking Tools And Software
- Hack Tools For Windows
- Hacking Tools Usb
- How To Make Hacking Tools
- Pentest Tools Online
- Hack Rom Tools
- What Are Hacking Tools
- Hacking Tools Name
- Hacker Techniques Tools And Incident Handling
- Hack Tools For Mac
- Pentest Tools Website
- Nsa Hacker Tools
- Hacking Tools Free Download
- Hacker Techniques Tools And Incident Handling
- Hack App
- Hack Tools
- Hack Website Online Tool
- Free Pentest Tools For Windows
- Pentest Tools Download
- Hacking Tools Mac
- Hacking Tools
- Tools For Hacker
- Hack Tools Pc
- Best Hacking Tools 2020
- Pentest Tools Find Subdomains
- Hacking Tools And Software
- Hacking Tools Mac
- Usb Pentest Tools
- Hacking Tools 2020
- Hacking Tools For Kali Linux
- Pentest Recon Tools
- Hacker Tools For Windows
- Hacker Hardware Tools
- Hacker Tools Hardware
- Hack Tools For Windows
- Hacking Tools For Mac
- Hack Tools Pc
- Hacking Tools For Kali Linux
- Hacking Tools Windows 10
- Hacking Tools Name
- Hacker Tools Free Download
- Hak5 Tools
- Hacker Tools 2020
- Tools 4 Hack
- Hacking Tools Download
- Hacker Tools Apk
- New Hack Tools
- Install Pentest Tools Ubuntu
- Pentest Tools Url Fuzzer
- Hacks And Tools
- Hacking Tools 2019
- Pentest Tools Linux
- Pentest Tools For Windows
- Best Hacking Tools 2020
- Hack Tools For Windows
- Pentest Tools

















No comments:
Post a Comment